Contact tracing tech
What is contact tracing and how is technology being used to improve it?
What are corporates doing? And why is adoption of contact tracing apps so challenging?
This project was completed in 2020 and is no longer being updated.
Kai Riemer, Raffaele Ciriello, Sandra Peter & Daniel Schlagwein (2020) Digital contact-tracing adoption in the COVID-19 pandemic: IT governance for collective action at the societal level, European Journal of Information Systems, DOI: 10.1080/0960085X.2020.1819898
What is contact tracing?
The COVID-19 pandemic has created a need for rapid, population-wide digital contact tracing.
Contact tracing is a public health practice to identify and notify those people who had contact with or visited the same locations as an infected person during their contagious period.
Manual contact tracing follows these steps:
- Obtain consent from the infected or suspected patient.
- Work with the patient to re-trace their whereabouts during the contagion period.
- List any contacts the patient interacted with.
- Visit places of potential contagion and notify exposed individuals and advise them what to do (e.g., get tested or self-isolate).
Manual contact tracing has certain shortcomings in fast-spreading viral outbreak. Recollection of patients might be poor, they might be unwilling to disclose information, tracing takes time and it is very labour intensive.
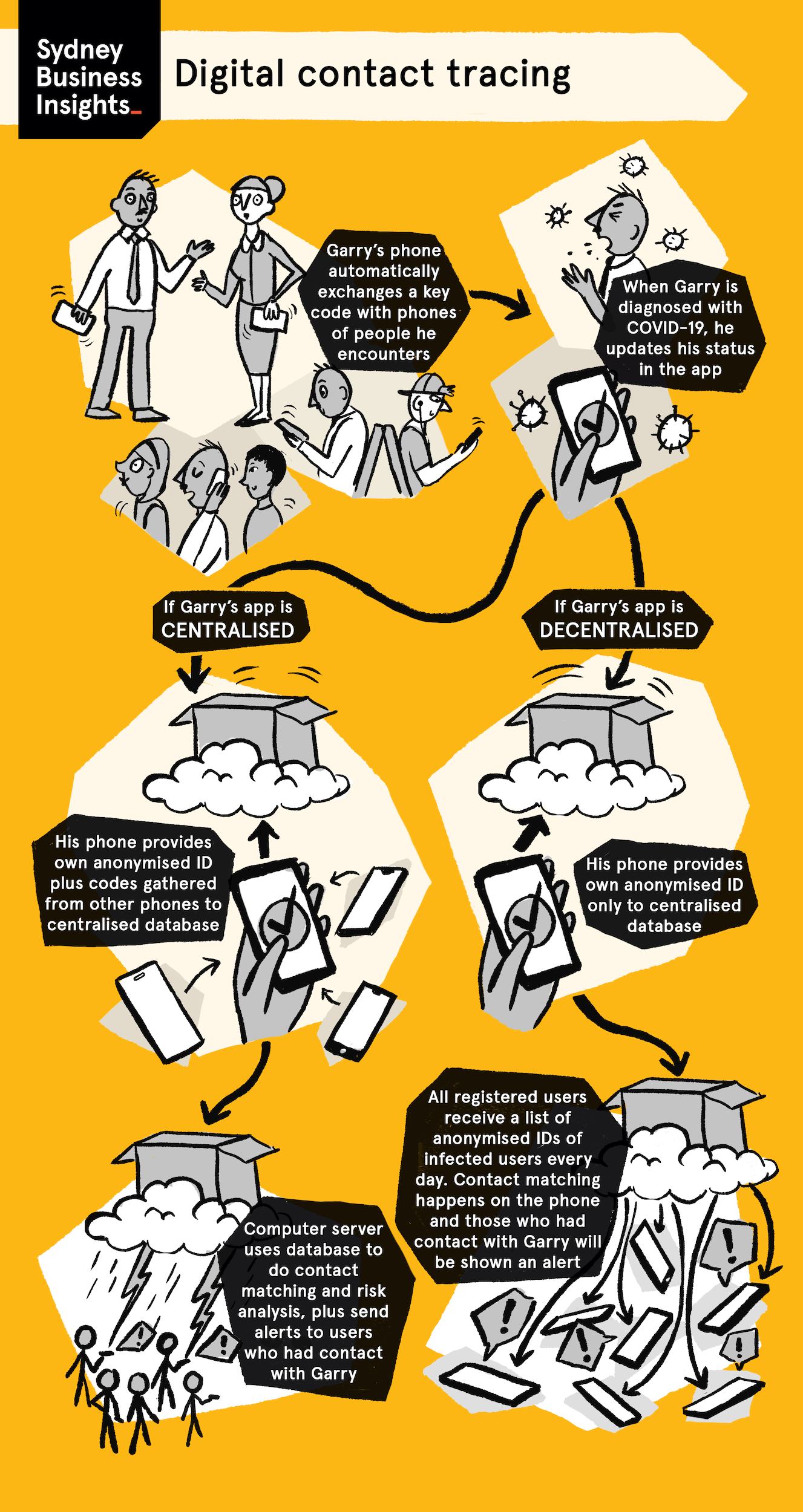
Digital contact tracing offers technology-supported solutions to alleviate some or all of the above shortcomings. Three different approaches exist, location-based tracing, centralised proximity tracing and decentralised proximity tracing.
Location tracing
Location tracing either uses a location-tracking app or is carried out top-down using a range of data and surveillance technologies to retrospectively retrace the movements and contacts of a newly diagnosed patient and identify those who frequented the same locations at the same time.
It might use a variety of digital data, such as GPS and cell phone locations, data from social media platforms, CCTV camera and facial recognition data, travel booking and transport data, and other data points. As a result, location tracing is considered highly privacy invasive. While successfully used in some countries it is considered intolerable or may even be illegal in many other societies, particularly Western ones.
Proximity tracing
Proximity tracing collects data while contacts between people take place, instead of tracing retrospectively,. It uses a smartphone’s Bluetooth technology to establish contact between two users by measuring distance (using signal strength) and duration of a contact. It works as follows:
- The user installs the service (e.g., via app download or OS update) on their smartphone and activates Bluetooth. The phone is registered with an ID at a central infection tracking server.
- The service operates in the background and acts as a beacon and receiver. It sends out its own ID and collects the IDs of other users located within a certain radius and time span.
- When a user tests positive, he/she tells the app. The service then registers the infection with the contact tracing server.
- All users the patient came in contact with receive a notification as well as instructions what to do.
There are two versions of proximity tracing that come with different privacy implications.
Centralised proximity tracing
Users register their phone number with a central computer server, which then creates the anonymized IDs that devices exchange. Anonymity is thus preserved between devices but not vis-à-vis the central authority (such as government health agencies). The central server is in charge of decrypting keys and contacting devices of exposed users via their phone numbers. This centralisation allows authorities to know who is infected and who was exposed, which can feed into manual contact tracing efforts.
Decentralised proximity tracing
Users register with the central server anonymously rather than with their phone number. Individual phones carry out much of the tracing and notification. Instead of centralized registration of exposed users and push notifications to devices, each device pulls all known IDs of infected users from the server and compares these with the decentral, locally held list on the device, which means the server does not need to know the identity of any device, infected user or those exposed. While the most privacy-preserving solution, it does not allow authorities access to exposure data, thus disconnecting the solution from manual contact tracing.
The most widely used technology is Apple and Google’s decentralised Exposure Notification service that underpins apps in many countries. Implementation at the operating system level ensures seamless functioning of apps with a device’s Bluetooth. While centralised solutions, like the Australian COVIDSafe app, are favoured by some governments because they intersect with manual contact tracing, they suffer from certain restrictions in accessing Bluetooth while phones are not in use, limiting their efficacy
| Approach | Example | Benefits | Drawbacks |
|---|---|---|---|
| Manual Contract Tracing | Common practice at prior pandemics, such as MERS, SARS1, or HIV. | Well understood, effective, accepted, and institutionalised. | Error-prone, time-intensive, labor-intensive, privacy- invasive, does not scale in rapid outbreaks. |
| Surveillance Tracing | South Korea’s “Virtuous Surveillance”. | Effective, top-down, comprehensive, no population acceptance needed. | Not suitable for individualistic societies, highly privacy invasive, risk of surveillance state. |
| Proximity Tracing (centralised) | Singapore’s “TraceTogether”, Australia’s “COVIDSafe” Apps. | Effective (if widely used), public sector controlled, integrates with manual tracing. | Privacy concerns toward governments, no automatic rollout possible |
| Proximity Tracing (decentralised) | Apple-Google’s Exposure Notification. | Effective (if widely used), global, not privacy invasive, infrastructure already in place, direct OS access, automatic rollout possible. | Private sector controlled, privacy concerns toward corporations, lack of public control and no integration with manual tracing. |
Contact tracing apps
The following table provides a structured overview of the digital contact tracing solutions used by countries around the world. We are comparing these solutions according to their technical approaches (see above), and in more detail, their privacy implications:
- Penetration / diffusion: percentage of the population using the app (at time of data collection)
- Tech: Bluetooth proximity tracing, or location-based tracing – see above for detailed descriptions
- Voluntary: Is the individual user free to adopt and resist adoption or is use mandated or centrally enforced?
- Centralisation: centralised vs decentralised (see above), location-based tracing is always centralised
Note: where cells are marked as TBD, we are actively looking for this information. If you are able to help, please get in touch.
Contact tracing around the world
Contact tracing in the US
In the United States every state creates their own individual contact tracing solution. Those solutions are not included in the above table. As most US states are still developing their solutions, the following table presents very much a work in progress.
Source: Sydney Business Insights (last updated, 13 October 2020.
Corporate contact tracing
A range of commercial products and services have been launched to help businesses and public organisations to safely re-open their premises. The following table gives an overview of the range of approaches that are being implemented; it is not meant to be exhaustive. It becomes obvious that privacy is less of concern in on-premise tracing, compared with the implementation of public solutions by governments and health agencies.
| # | Type of tracing | Description | Examples |
|---|---|---|---|
| 1 | Check-in tracing | Keeping a log of everyone who visits a location, such as an office or restaurant, allows notifying potentially exposed contacts, if someone in attendance tests positive. | CovidPass: Simple QR code solution for small businesses SwipedOn: Add-on to professional visitor management system |
| 2 | Proximity tracing | Solutions that establish contacts by way of proximity between devices. | |
| 2a) Smartphone App | Commercial smartphone apps that implement Bluetooth-based proximity tracing for on-premise use by an organisation’s employees | Mobile Programming, SaferMe, PwC: bespoke smartphone apps for corporate clients | |
| 2b) Tokens and badges | Bluetooth-based proximity-tracing implemented without smartphone app, using physical devices that collect the contact data and transmit it to a central server. | Estimote: New product by IoT tracking start-up | |
| 3 | Location tracing | Solutions that track employees’ whereabouts while on premise. | |
| 3a) Tokens and beacons | Beacons installed in the environment collect data from Bluetooth tokens (badges), thus mapping a user’s locations for contact tracing. | LeashIT: New service by asset tracking company Estimote: New product by IoT tracking start-up | |
| 3b) GPS and WiFi | Smartphone apps that don’t use Bluetooth proximity tracing, but determine a user’s (approximate) location on premise using GPS and/or WiFi data. | New Mexico State University: students developed an app for on campus use, tracking smartphone locations | |
| 4 | Surveillance tracing | Most comprehensive (and intrusive) form of contact tracing. Combines a range of surveillance data, such as badge scan, wifi data, meeting bookings, work shift logs etc, to determine location and potential contacts. | ServiceNow: Safe Workplace suite comes with integration of multiple data points. |
| 5 | Integrated solutions | Comprehensive systems combining a number of tracing methods, usually with integrated dashboards. | Ramco: Comprehensive check-in, tracing and tracking add-ons to workforce management suite Zyter: Integrated health facility management system for nursing homes and clinics, comes with check-in and other means of tracing |
Challenges of contact tracing adoption
Pandemics such as COVID-19 present large-scale crises that require collective action at the societal level to be contained, including the use of digital technologies.
The following research paper discusses in detail the challenges of contact tracing adoption and proposes a framework for governments and health agencies to govern the roll-out and adoption of, in particular privacy-preserving Bluetooth-based proximity tracing.
Digital Contact Tracing Adoption in the COVID-19 Pandemic: IT Governance for Collective Action at the Societal Level
By Kai Riemer, Raffaele Ciriello, Sandra Peter, Daniel Schlagwein
https://doi.org/10.1080/0960085X.2020.1819898
Abstract
The COVID-19 pandemic has created a need for rapid, population-wide digital contact tracing. One solution, Bluetooth-enabled digital proximity tracing using smartphones, promises to preserve individual privacy while helping to contain society-wide viral outbreaks. However, this digital solution works effectively only if adopted by the majority of the population. This poses a collective action problem: everyone would benefit from wide-spread proximity tracing, but the benefits for the individual are indirect and limited. To facilitate such collective action at the societal level, this paper conceptualizes the option space of IT governance actions for proximity tracing adoption along two dimensions: decision-making entities (who will govern the roll-out) and accountability enforcement (how strictly will adoption and use be enforced). Examining coherent governance approaches that arise from the framework, we show that there are no globally ideal approaches but only locally contextualized ones that depend on immediate health risk, prior experience with pandemics, societal values and national culture, role of government, trust in government and trust in technology in each society. The paper contributes specific propositions for governing digital contact tracing in the COVID-19 pandemic and general theoretical implications for IT governance for collective action at the societal level.
Allison, S. T., & Kerr, N. L. (1994). Group Correspondence Biases and the Provision of Public Goods. Journal of Personality and Social Psychology, 66(4), 688-698.
Apple. (2020a). Apple and Google Partner on COVID-19 Contact Tracing Technology
Apple. (2020b). Privacy-Preserving Contact Tracing
Asghar, H., Farokhi, F., Kaafar, D., & Rubinstein, B. (2020). On the Privacy of TraceTogether, the Singaporean CVOID-19 Contact Tracing Mobile App, and Recommendations for Australia
ASHM. (2016). Australasian Contact Tracing Guidelines
Axelrod, R., & Hamilton, W. D. (1981). The Evolution of Cooperation. Science, 211(4489), 1390-1396.
Boonstra, A., Eseryel, U. Y., & van Offenbeek |, M. A. G. (2018). Stakeholders’ Enactment of Competing Logics in IT Governance: Polarization, Compromise or Synthesis? European Journal of Information Systems, 27(4), 415-433.
Busvine, D., & Rinke, A. (2020). Germany Flips to Apple-Google Approach on Smartphone Contact Tracing
Cellan-Jones, R. (2020). Contact tracing app ‘working in Ireland’
Cellan-Jones, R., & Kelion, L. (2020). Coronavirus: The Great Contact-Tracing Apps Mystery
Chen, D. Q., Preston, D. S., & Xia, W. (2010). Antecedents and Effects of CIO Supply-side and Demand-side Leadership: A Staged Maturity Model. Journal of Management Information Systems, 27(1), 231-272.
Chhokar, J. S., Brodbeck, F. C., & House, R. J. (2007). Culture and Leadership Across the World: The GLOBE Book of In-depth Studies of 25 Societies. Lawrence Erlbaum.
Consultancy.asia. (2020). Singaporean Attitudes to Personal COVID Data Differ to Overseas Counterparts
Criddle, C., & Kelion, L. (2020). Coronavirus Contact Tracing: World Split Between Two Types of App
Dalzell, S., & Probyn, A. (2020). Convincing Australians to Use Government-sponsored Coronavirus-tracing App a Tough Ask
Dave, P. (2020a). Explainer: How Smartphone Apps Can Help ‘Contact Trace’ the New Coronavirus
Dave, P. (2020b). Google says 20 US states, territories ‘exploring’ contact tracing apps
Dawes, R. M. (1980). Social Dilemmas. Annual Review of Psychology, 31, 169-193.
Dawson, G. S., Denford, J. S., Williams, C. K., Preston, D., & Desouza, K. C. (2016). An Examination of Effective IT Governance in the Public Sector Using the Legal View of Agency Theory. Journal of Management Information Systems, 33(4), 1180-1208.
de Reuver, M., Sørensen, C., & Basole, R. C. (2018). The Digital Platform: A Research Agenda. Journal of Information Technology, 33(2), 124-135.
Edelman. (2019a). Trust Barometer – Global Report
Edelman. (2019b). Trust Barometer – Trust in Technology
Etherington, D. (2020). Apple launches COVID-19 ‘Exposure Notification Express’ with iOS 13.7 — Android to follow later this month
Fama, E. F., & Jensen, M. C. (1983). Separation of Ownership and Control. The journal of Law and Economics, 26, 301–325.
Farrell, P. (2020). Experts Raise Concerns about Security of Coronavirus Tracing App COVIDSafe
Fedorowicz, J., Sawyer, S., & Tomasino, A. (2018). Governance Configurations for Inter-organizational Coordination: A Study of Public Safety Networks. Journal of Information Technology, 33(4), 326-344.
Ferretti, L., Wymant, C., Kendall, M., Zhao, L., Nurtay, A., Abeler-Dörner, L., Parker, M., Bonsall, D., & Fraser, C. (2020). Quantifying SARS-COV-2 Transmission Suggests Epidemic Control with Digital Contact Tracing. Science, 368(6491).
Garthwaite, R., & Anderson, I. (2020). Coronavirus: Alarm over ‘Invasive’ Kuwait and Bahrain Contact-Tracing Apps
Ghazawneh, A., & Henfridsson, O. (2015). A Paradigmatic Analysis of Digital Application Marketplaces. Journal of Information Technology, 30, 198-208.
Gladstone, N. (2020). COVIDSafe App Yet to Trace Useful Number of Unique Cases Despite Second Wave
Graham-Harrison, E. (2020). Coronavirus: How Asian Countries Acted While the West Dithered
Grant, G., & Tan, F. B. (2013). Governing IT in Inter-organizational Relationships: Issues and Future Research. European Journal of Information Systems 22(5), 493-497.
Gregory, R. W., Kaganer, E., Henfridsson, O., & Ruch, T. J. (2018). IT Consumerization and the Transformation of IT Governance. MIS Quarterly, 42(4), 1225-1253.
Guillemette, M. G., & Paré, G. (2012). Toward a New Theory of the Contribution of the IT Function in Organizations. MIS Quarterly, 36(2), 529-551.
Hamm, J. A., Smidt, C., & Mayer, R. C. (2019). Understanding the Psychological Nature and Mechanisms of Political Trust. PLoS ONE, 14(5).
Haskins, C. (2020). Workers Around the World Are Already Being Monitored By Digital Contact Tracing Apps
Hofstede, G. (1980). Culture’s Consequences: International Differences in Work-related Values. Sage.
Hofstede, G. (2001). Culture’s Consequences: Comparing Values, Behaviors, Institutions, and Organizations Across Nations (2e). Sage.
Horowitz, J., & Satariano, A. (2020). Europe Rolls out Contact Tracing Apps, with Hope and Trepidation
House, R. J., Hanges, P. J., Javidan, M., Dorfman, P., & Gupta, V. (2004). Culture, Leadership, and Organizations: The GLOBE Study of 62 Societies. Sage.
Howell O’Neill, P. (2020a). Apple and Google’s COVID-Tracing Tech Has Been Released to 23 Countries
Howell O’Neill, P. (2020b). Bluetooth Contact Tracing Needs Bigger, Better Data
Howell O’Neill, P. (2020c). No, Coronavirus Apps Don’t Need 60% Adoption to Be Effective
Howell O’Neill, P. (2020d). Norway Halts Coronavirus App Over Privacy Concerns
Huang, R., Zmud, R. W., & Price, L. R. (2010). Influencing the Effectiveness of IT Governance Practices Through Steering Committees and Communication Policies. European Journal of Information Systems, 19(3), 288-302.
Huang, Y., Sun, M., & Sui, Y. (2020). How Digital Contact Tracing Slowed COVID-19 in East Asia
Kelion, L. (2020a). Apple and Google Accelerate Coronavirus Contact Tracing Apps Plan
Kelion, L. (2020b). Coronavirus: France’s Virus-tracing App ‘Off to a Good Start’
Kelion, L. (2020c). Coronavirus: Ministers Consider NHS Contact-tracing App Rethink
Kim, M. J., & Denyer, S. (2020). A ‘Travel Log’ of the times in South Korea: Mapping the Movements of Coronavirus Carriers
Kim, M. S. (2020). Seoul’s Radical Experiment in Digital Contact Tracing
Lacity, M., & Hirschheim, R. (1993). The Information Systems Outsourcing Bandwagon. MIT Sloan Management Review, 35(1), 73-86.
Lankton, N. K., McKnight, D. H., & Tripp, J. (2015). Technology, Humanness, and Trust: Rethinking Trust in Technology. Journal of the Association for Information Systems, 16(10), Article 1.
Law, E. (2020). Coronavirus: China’s Contact Tracing App Touted as Helping to Contain Outbreak
Lazar, S., & Sheel, M. (2020). Contact Tracing Apps Are Vital Tools in the Fight Against Coronavirus. But Who Decides How They Work?
Leclercq-Vandelannoitte, A., & Bertin, E. (2018). From Sovereign IT governance to Liberal IT Governmentality? A Foucauldian Analogy. European Journal of Information Systems, 27(3), 326-346.
Leidner, D. E., & Kayworth, T. (2006). A Review of Culture in Information Systems Research: Toward a Theory of Information Technology Culture Conflict. MIS Quarterly, 30(2), 357-399.
Leswing, K. (2020). Companies Could Require Employees to Install Coronavirus-tracing Apps like This One from Pwc Before Coming Back to Work
Li, J., & Guo, X. (2020). COVID-19 Contact-tracing Apps: A Survey on the Global Deployment and Challenges
Lomas, N. (2020). How Will Europe’s Coronavirus Contact-tracing Apps Work Across Borders?
Loveboy, B. (2020a). EU Rejects Idea of Making Contact Tracing Apps Mandatory for Travel
Loveboy, B. (2020b). Poll: Would You Agree to Coronavirus Contact Tracing If It Were Done by Apple?
Magnusson, J., Koutsikouri, D., & Päivärinta, T. (in press). Efficiency Creep and Shadow Innovation: Enacting Ambidextrous IT Governance in the Public Sector. European Journal of Information Systems.
McKnight, D. H., Carter, M., B., T. J., & Clay, P. F. (2011). Trust in a Specific Technology: An Investigation of Its Components and Measures. ACM Transactions on Management Information Systems, 2(2), 12-32.
Mindel, V., Mathiassen, L., & Rai, A. (2018). The Sustainability of Polycentric Information Commons. MIS Quarterly, 42(2), 607–632.
Mintzberg, H., & McHugh, A. (1985). Strategy Formation in an Adhocracy. Administrative Science Quarterly, 30(2), 160-197.
Moldoveanu, M., & Martin, R. (2001). Strategy Formation in an Adhocracy
Morley, J., Cowls, J., Taddeo, M., & Floridi, L. (2020). Ethical Guidelines for COVID-19 Tracing Apps. Nature, 582, 29-31.
Mulgan, R. (2000). Accountability: An Ever-expanding Concept? Public Administration, 78, 555–573.
Newton, C. (2020). Why Bluetooth Apps Are Bad at Discovering New Cases of COVID-19
Nolan, D. (1971). Classifying and Analysing Politico-economic Systems. The Individualist, 1, 5-11.
Olson, M. (1965). The Logic of Collective Action: Public Goods and the Theory of Groups. Harvard University Press.
Ostrom, E. (1990). Governing the Commons: The Evolution of Institutions for Collective Action. Cambridge University Press.
Palmer-Derrien, S. (2020). ‘Turn the Angry-mob Mode Off’: Cannon-Brookes Calls on Divided Tech Industry to Back Government’s COVIDSafe App
Phartiyal, S. (2020). India Orders Coronavirus Tracing App for All Workers
Provan, K. G., & Kenis, P. (2008). Modes of Network Governance: Structure, Management, and Effectiveness. Journal of Public Administration Research and Theory, 18(2), 229-252.
Rivero, N. (2020). Global contact tracing app downloads lag behind effective levels
Roper, W. (2020). Americans Split on Contact Tracing App
Scott, D. (2020). What Good Digital Contact Tracing Might Look Like
Slonim, R. (2020). In Some Places 40% of Us May Have Downloaded COVIDSafe: Here’s Why the Government Should Share What It Knows
Statista. (2020). Mobile Operating Systems’ Market Share Worldwide from January 2012 to December 2019
Sun, K., & Viboud, C. (2020). Impact of Contact Tracing on SARS-COV-2 Transmission
Taylor, J. (2020). Coronavirus Apps: How Australia’s COVIDSafe Compares to Other Countries’ Contact Tracing Technology
Thaler, R. H., & Sunstein, C. R. (2009). Nudge: Improving Decisions about Health, Wealth, and Happiness. Penguin.
Thompson, D. (2020). The Technology That Could Free America From Quarantine
Thöni, C., & Volk, S. (2018). Conditional Cooperation: Review and Refinement. Economics Letters, 171, 37-40.
Tidy, J. (2020). Coronavirus: Israel Enables Emergency Spy Powers
Trang, S., Trenz, M., Weiger, W. H., Tarafdar, M., & Cheung, C. M. K. (2020). One App to Trace Them All? Examining App Specifications for Mass Acceptance of Contact-tracing Apps. European Journal of Information Systems.
Urbaczewski, A., & Lee, Y. J. (2020). Information Technology and the pandemic: a preliminary multinational analysis of the impact of mobile tracking technology on the COVID-19 contagion control. European Journal of Information Systems.
Wagner, D., & Rogers, J. (2020). China’s Coronavirus Success Shows up Poor Pandemic Preparedness in the Rest of the World
Wareham, J., Fox, P. B., & Cano Giner, J. L. (2014). Technology Ecosystem Governance. Organization Science, 25(4), 1195–1215.
Weill, P. (2004). Don’t Just Lead, Govern: How Top-performing Firms Govern IT. MIS Quarterly Executive, 3, 1-17.
Weill, P., & Ross, J. W. (2004). IT Governance: How Top Performers Manage IT Decision Rights for Superior Results. Harvard Business Press.
Weinmann, M., Schneider, C., & vom Brocke, J. (2016). Digital Nudging. Business & Information Systems Engineering, 58(6), 433–436.
Weitzner, D. J., Abelson, H., Berners-Lee, T., Feigenbaum, J., Hendler, J., & Sussman, G. J. (2008). Information Accountability. Communications of the ACM, 51(6), 82-87.
Xiao, J., Xie, K., & Hu, Q. (2013). Inter-firm IT Governance in Power-imbalanced Buyer–supplier Dyads: Exploring How It Works and Why It Lasts. European Journal of Information Systems, 22(5), 512-528.
Yun, M. (2020). How Taiwan Is Containing Coronavirus – Despite Diplomatic Isolation by China
Zastrow, M. (2020). South Korea Is Reporting Intimate Details of COVID-19 Cases: Has It Helped?
This resource is part of a series of insights related to COVID-19 and its impact on business.